Ransomware Threatens to Hold Health Care Companies Hostage
Never miss a thing.
Sign up to receive our insights newsletter.
One of the fastest growing cybercrimes out there, ransomware, hits the health care industry particularly hard because in many cases it can be a matter of life and death. If health care workers cannot access medical records, their ability to treat patients is severely impacted.
Ransomware is particularly dangerous to health care organizations because although it is a common variety of malware, the attacker is not seeking to extract data. Ransomware works by encrypting the data within the breached system, preventing organizations from accessing the data and critical systems without the encryption key, which is held by the attacker. The attackers then demand a sum of money to provide the key to decrypt the data; usually, they require that the fee be remitted in a cryptocurrency such as bitcoin. Refuse to pay, and you may not be able to access your data or systems in the near term, if at all. Pay the ransom, and you create a bigger market for this type of attack.
A ransomware attack on a health care organization is considered a data breach under the Health Insurance Portability and Accountability Act (HIPAA) because when electronic health information (ePHI) is encrypted as a result of a ransomware attack, the data is technically acquired (i.e., an unauthorized person has taken possession or control of the data). As a result, the health care organization will be required to issue notification of the breach unless it can demonstrate there is a low probability that the ePHI has been compromised.
Slow adoption of electronic data solutions has left health care organizations behind the curve
In most industries, digital recordkeeping has been the norm since the 1990s. But health care was late to the game for a number of reasons, including physician resistance, comfort with a paper-based system and inadequate funding. In 2008, according to a 2009 study in the New England Journal of Medicine, fewer than 2% of the nation’s health care providers had adopted a comprehensive electronic health record (EHR) system and only 8% had adopted even a purpose-built EHR system.
Change eventually came in response to monetary incentives by the Center for Medicare and Medicaid Services’ Meaningful Use Program as well as increased awareness of the advantages of going digital as the use of single source of data, reduced paper storage and ease of sharing between providers.
Fast forward to 2020, and we now see a nearly universal adoption of EHR systems. With this widespread adoption come different threats to the industry, and the health care industry is catching up with the curve in confronting these threats. Enter ransomware.
Ransomware is lucrative for attackers, and health care organizations are likely to continue to be prime targets for ransomware attacks for several reasons:
- Health care organizations are typically less secure from an infrastructure perspective because the industry as a whole has been behind in adopting electronic data storage as well as proper cybersecurity standards
- Hospitals are six times more likely to internally host their data, putting the responsibility for keeping up with an ever-changing threat landscape on hospital employees rather than third parties that may be better equipped to do so
Data lockdown can be life threatening to patient care or treatment courses, causing more panic when an attack does hit.
Is this a real threat?
Yes! Based on a recent study by EMSISOFT, at least 41 hospitals and other healthcare providers have reported being victims of ransomware in Q1 and Q2 of 2020. Prior to that, according to a report from Corvus there was a 350% increase in ransomware attacks on healthcare entities in Q4 2019 vs. Q4 2018.
Here are some other examples of ransomware attacks reported in 2019:
- The Cancer Center of Hawaii announced on December 11 that it had to suspend cancer radiation services at two treatment centers due to a ransomware attack.
- All three Tuscaloosa-based DCH Health System hospitals temporarily closed to new patients due to a targeted ransomware attack.
- Wood Ranch Medical announced that it would close in December after a ransomware attack caused the Simi Valley, California-based medical clinic to lose all access to its patients’ medical records. The clinic closed December 17, 2019.
- Pleasant Grove, Utah-based Premier Family Medicine alerted 320,000 patients that their health information may have been exposed in a ransomware attack.
How to prepare, prevent and recover
Health care organizations should take the following steps to prepare, prevent and recover from a ransomware attack.
Understand how malware is entering your environment.
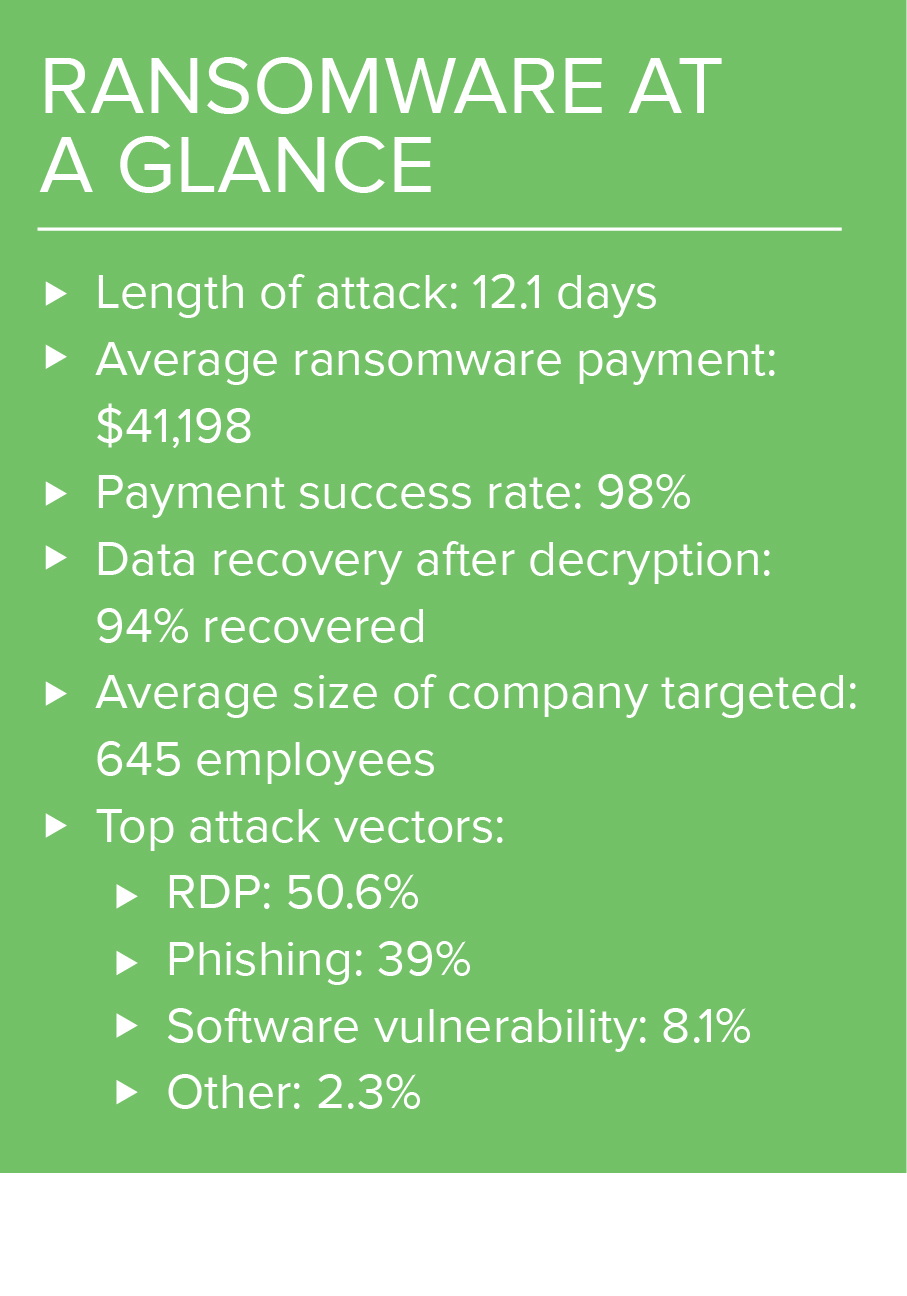
The two most common ransomware attack vectors are Remote Desktop Protocol (RDP) and email phishing. According to Coveware’s 2019 Q3 Ransomware Marketplace report, RDP-based breaches accounted for 50.6% of the ransomware cases handled by their support team, and 39% of them were a result of email phishing.
Reduce the risk and strengthen RDP and email security.
- Put RDP servers behind a firewall
- Require strong RDP passwords
- Employ two-factor authentication for RDP
- Run regular vulnerability scans
- Remediate vulnerabilities when identified by scans
- Train users on best email security practices
- Use email scanning and filtering tools
- Test users with email specific social engineering tests
The system’s users are among the biggest security risks, so take time to invest in their training on both the use of the technologies as well as the user’s role in security within the organization.
Implement immutable backups.
In other words, ensure that backups cannot be modified. This step will allow you to restore data quickly in the event of a ransomware attack and protect backup data from being impacted by a ransomware attack.
Review and update incident response protocols.
Make sure a plan is in place to quickly detect and respond to suspicious activity that can lead to a ransomware attack.
Invest in cyber insurance.
Having coverage can help an organization financially recover from an attack if they are unfortunate enough to be the target of one.
By taking these steps to evaluate their risk and implement proper controls to mitigate them, health care organizations will be able to continue to focus on their primary mission: providing quality care for their patients.
If you would like to better understand how your health care organization can protect its data and systems from ransomware or other cyberattacks, we welcome you to contact Weaver’s IT Advisory Services team. With a focus on health care, we understand the unique needs and concerns of your organization and are available to help.
© 2020