A Roadmap to PCI DSS Compliance
Related
Never miss a thing.
Sign up to receive our insights newsletter.
Perhaps your sales team has told you that the product or service you are selling now has to be PCI (Payment Card Industry) compliant. Or your credit card processor has informed your organization that you need be PCI compliant. You’ve heard pursuing PCI compliance is full of headaches. As you flip through the PCI DSS (Data Security Standard), you find that the requirements your company may have to meet seem overwhelming. Does this sound familiar?
Many organizations that accept credit cards are required to comply with the PCI DSS. With 12 requirements and more than 250 sub-requirements, the process can sound daunting. Often, organizations who first try to meet the requirements internally through a self-assessment process later find, after hiring a PCI Qualified Security Assessor (QSA), there are compliance gaps with requirements they thought were in place. For example, the self-assessment may have interpreted key requirements incorrectly or internal documentation may not be up to PCI standards.
To drive your compliance efforts in the right direction, here are some steps you can take:

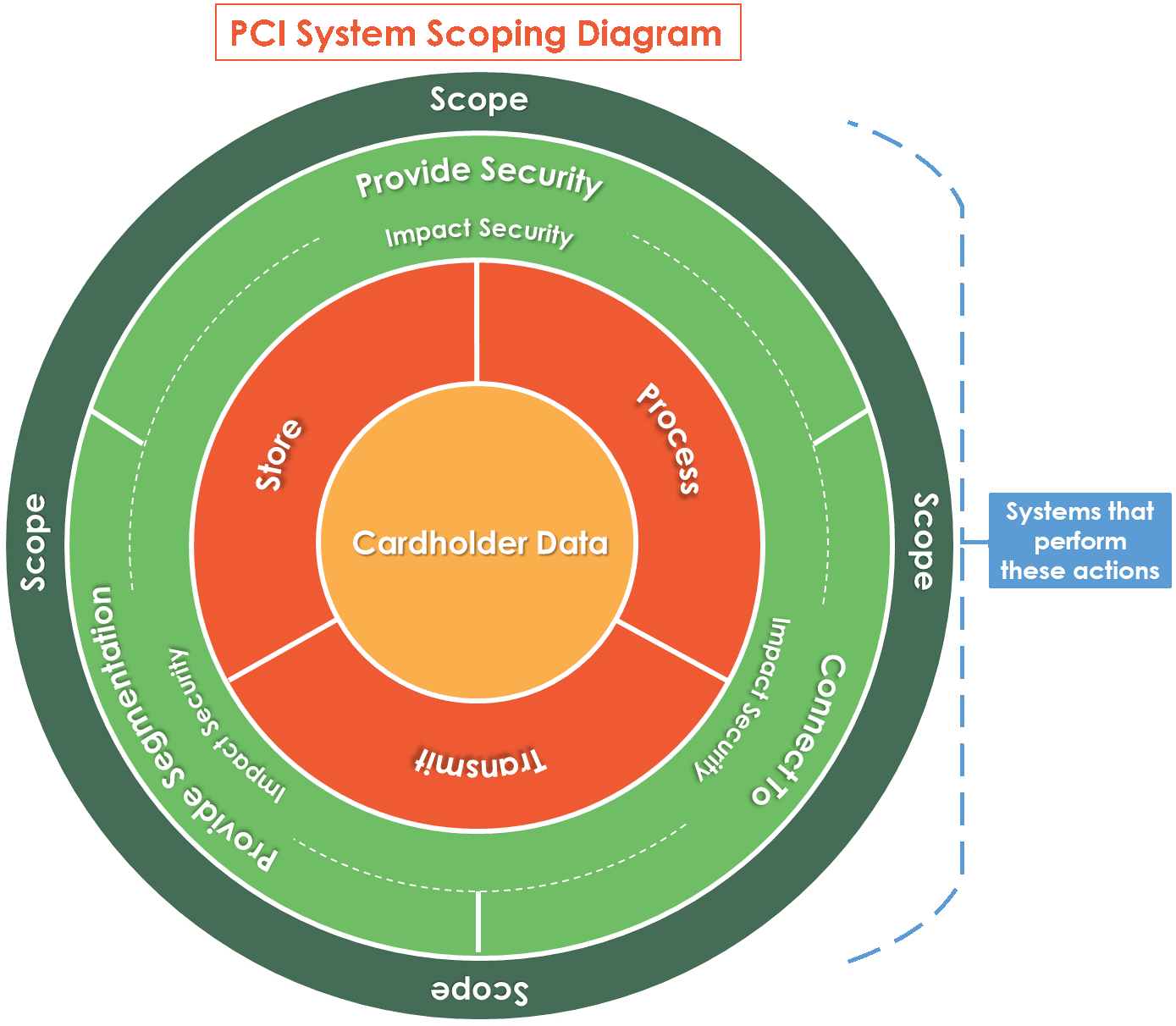
Define the cardholder data environment (the scope of a PCI assessment). Identifying the scope is the most important part of the audit process. This may seem simple, but often it determines the success or failure of a PCI engagement. PCI defines the cardholder data environment (CDE) as those people, processes, or technologies that store, process, transmit, or could affect the security of cardholder data. This broad criteria could make large portions of an organization’s environment subject to the assessment, so it is important to understand which tools and technologies, such as VLAN segmentation, can reduce the size of the CDE.

Get to the heart of the requirement. Make sure you understand each requirement, and if you have questions, read the Guidance column in the DSS. Looking at a single requirement in isolation without considering them alongside the whole document can lead to misunderstandings about what is actually required. PCI requirements are specific and not meant to be subjective.

Understand evidence requirements. Unlike other compliance audits, PCI requires a QSA to perform specifically prescribed testing procedures that outline the types of evidence that must be available for review. To understand the evidence detail and depth required to achieve compliance, review the test procedures in the Report on Compliance (RoC) template, which is the primary report the QSA completes during an assessment.

Take a risk-based implementation approach. With more than 250 sub-requirements, even well-resourced organizations may find that implementing the right combination of these is a tall order. To make the process easier, the PCI Security Standards Council (SSC) has developed a Prioritized Approach tool, which is available in the PCI Document Library. The tool categorizes each sub-requirement by milestone, based on risk and getting the biggest “bang for your buck” in terms of security exposure while allowing your organization to track and report on your PCI DSS implementation progress.

Engage a QSA company to complete a readiness assessment. Without proper planning, a complete PCI DSS assessment can be painful. A good way to ensure your organization is on the right track before diving into a full blown assessment is to have a firm with experienced QSAs first perform a readiness assessment. This gives your organization a taste of a full PCI DSS assessment, aligns expectations between the QSA and your organization, and gives your organization time to identify and remediate gaps prior to the actual audit.
The road to PCI DSS compliance can be painful. But taking a methodical approach can set your organization up for success during its PCI journey. Weaver has assisted a wide range of organizations, including small businesses and Fortune 50 enterprises, in applying the DSS to their environment. To find out how Weaver can help your organization achieve and maintain PCI DSS compliance, or strengthen your security program in general, contact us. We are here to help.
© 2020