Staying out of the Headlines: Takeaways from the 2020 DBIR Report
Never miss a thing.
Sign up to receive our insights newsletter.
The 2020 Verizon Data Breach Investigations Report is here! Verizon produces this annual report, DBIR for short, to identify trends in known incidents and data breaches over the past year. The 2020 report analyzed 157,525 reported incidents and 3,950 confirmed data breaches across many different industries. While no business wants to be the subject of a story like this, we can all learn and take immediate action based on the experiences described in the report.
When most people think of ‘hacking’ they probably think of a computer ‘virus’ or a computer whiz writing thousands of lines of code to break into the most sophisticated of systems and steal money and secrets. Or they may picture a high-school kid breaking into the Pentagon’s WOPR computer to play simulated war games. Yes, we’re talking about the 1983 movie “War Games.”
But in reality, most modern day data breaches are much simpler and can be mitigated with common sense controls and processes.
According to the DBIR, in 2020, 67% of all confirmed breaches were due to user credentials being leaked, misconfiguration in cloud assets and web applications, and social engineering attacks such as phishing. In 43% of those breaches the primary vector of attack was a web application.
The weakest links in organizations are:
- People
- Improperly developed web applications
- Misconfiguration
- Lack of defense in depth
This graphic illustrates how the methods of ‘hacking’ have changed over the last five years.
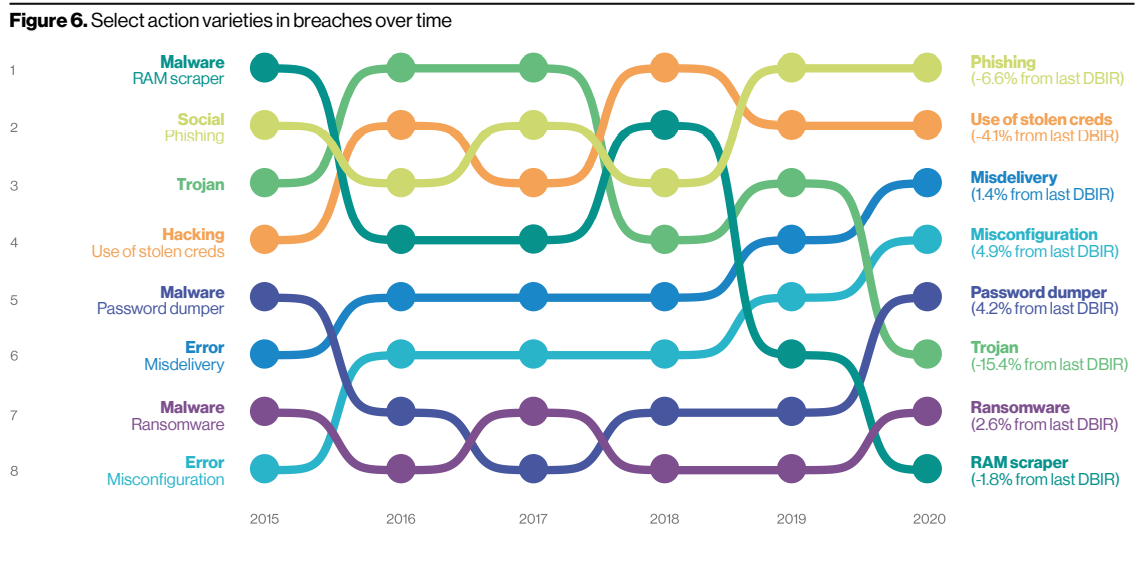
Source: Verizon 2020 Data Breach Investigations Report
Executives often recognize the value in a resource like the DBIR, but they may either react too aggressively or not know where to start. So what action should you take on behalf of your organization? Here are some baseline questions that you should be asking your IT and cybersecurity teams.
- Training. Do our people get the appropriate training around cybersecurity?
- Layered Access. Do we have mechanisms in place, such as multi-factor authentication, to mitigate the exposure when our people make mistakes?
- Defense with Stats. Do our web applications, which have back-end access to some of the most sensitive data in our organization, have the appropriate defenses in-front of them to block the most common of web application security risks? And can we demonstrate when they work and when they fail?
- Talent. Do we have the appropriate skills in-house to properly develop and secure modern web applications?
- Crystal Clear Playbook. Do we have clearly defined hardening and configuration standards and practices to secure our organization? Is it consistently applied?
- Effective Layers. Does our organization have a layered strategy towards security or do we rely on one or two magic bullets to solve all of our security needs?
These areas and questions are a place to start, but as you dive deeper into the DBIR, let Weaver know if we can help you navigate the ever changing world of cybersecurity.
Contact us to learn more about Weaver’s IT and Security services.
© 2020