Cybersecurity Questions Board Members Should Be Asking Management
Never miss a thing.
Sign up to receive our insights newsletter.

Cybersecurity risk is regularly on the list of critical topics for Boards to consider. But all too often, Board members need more information to fully understand the actual risks or actions the organization is taking to mitigate them. Not only that, specific steps to resolve cybersecurity risks may not align with the organization’s cyber program.
A Board can set the tone for strong cybersecurity practice throughout the organization. Once Boards understand that security is not a new, novelty issue but rather a foundational responsibility, the Board and leadership can work together to ensure security is well incorporated into the organization’s larger cyber program. Furthermore, by emphasizing cybersecurity, the Board helps bring visibility to cyber-based initiatives that management can action.
Communication must be a two way street. Just as it wouldn’t settle for only part of the balance sheet, cash flows and income statement, the Board needs a complete presentation of the organization’s cybersecurity program to review the elements as whole. All too often, however, the Board receives an incomplete picture that does not foster a meaningful exchange between the Board and Management.
Management should regularly update the Board with strategic, measurable information. Management and executive leaders should ensure that the board is equipped and has access to expertise and resources to answer, at a minimum, these three key areas:
- What is the attack surface or cyber footprint?
- What are the risks?
- What are we doing about it?
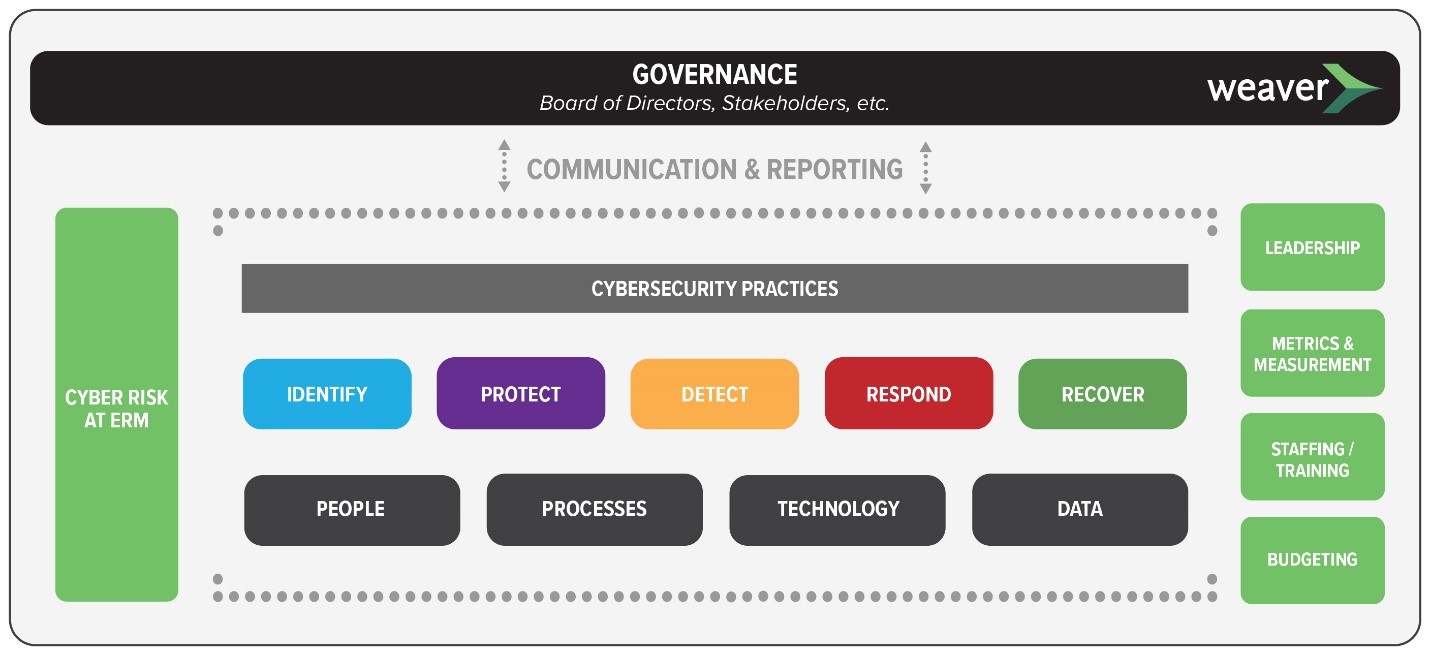
The following graphic provides a high-level perspective of cybersecurity across an organization. This helps facilitate communication and discussion among individuals with different backgrounds over a subject that has many facets.
Here are questions for Board members to consider in reviewing information about the organization’s cybersecurity program:
Is the information complete and what does it reflect about the actual risk to the organization?
A report that an organization’s firewall “blocked 50,000 attacks” does not offer a complete picture. Additional detail is required to understand the context and applicable risk. Where is the firewall placed? What is it protecting? How many attacked weren’t blocked? Are there other ingress/egress points? Without complete information, the Board cannot fully address areas of cybersecurity risk.
Is the information communicated frequently enough?
As cybersecurity threats rise, presenting information as only part of an annual update is not sufficient. While time may not permit regular discussion of cybersecurity, Boards should receive frequent updates with consistent metrics and measures that have been defined, explained and agreed upon.
Does the Board understand information regarding accountability, industry framework for practices and controls, compliance considerations, and sufficient training?
Leadership & Staffing: Are sufficient personnel assigned to monitor and prevent cybersecurity threats from occurring in the first place?
Cybersecurity should not be an afterthought, scrutinized only in response to a security incident that has already taken place. It is important to have a clear understanding regarding who is responsible and accountable to manage cyber risk and related issues. Framework: Mature organizations codify their practices in formal controls that are aligned with an established cybersecurity framework. These practices are incorporated into the organization’s day-to-day operations. Which industry-accepted framework is the organization aligned with?
Compliance: Which security regulations does the organization need to comply with?
Awareness, monitoring and reporting should be proactively measured and communicated.
Training: Are front line defenders being provided with regular updates?
With rapid changes in technology, organizations need to ensure that individuals responsible for enforcing security stay up-to-date through adequate training.
Does the organization track cybersecurity and correlate it at the Enterprise Risk level?
This is where the adage “There are no IT risks, only business risks” comes into play. Successful organizations are able to articulate cyber risk in context based on their goals and objectives. An initial step is to track and incorporate cybersecurity risk into the ERM program to ensure visibility and awareness.
Once these basic questions are answered and understood, cybersecurity can be evaluated in relation to other significant operations and events, such as:
- Supply chain and vendor dependencies
- Mergers and acquisitions
- Response to a security incident
- Financial impact and cyber insurance
Even if an organization is still developing consistent and informative communications between the Board and management, key activities may be performed. These practices need to be analyzed and placed in context to provide a perspective that aligns with the organization’s goals and objectives.
If you are working on your cyber program, we welcome you to contact us for best practices on Board communication and managing cyber risks.
© 2021
